Keeping your computer's firewall on is probably the best alternative if you are new to technology, but in some situations you will need to know how to turn it on or off. So here is a simple guide to help you do that..
A firewall is a security barrier that defines what traffic is allowed to enter your computer over a network. Usually, a firewall allows good traffic to pass, while preventing hackers, malware, and other suspicious traffic from accessing your computer.
Most routers have built-in firewalls. Therefore, if you are using a router (which most people do), you already have good protection against outside threats. You also have a firewall on your computer, usually built into Mac OS X. But this is not as important as your router's firewall, and sometimes it is necessary to turn it off in certain situations. For example if you have installed antivirus software that has its own firewall, or if you want to run a program that does not work properly because it conflicts with your computer's firewall. If for some reason you need to turn off your Mac's firewall, then you can continue reading this article..
Clean up a Mac before changing settings
Before we see how you can turn the firewall on and off, we strongly recommend that you clean up the apps on your Mac, especially the ones you recently uninstalled. If you downloaded an application by mistake and uninstalled it or found a malicious application on your computer and moved it to the trash, then there is a good chance that traces of these applications still exist on your system.
If it does and the firewall is turned off, then these apps will be able to send and receive traffic, putting your Mac at serious risk..
Therefore, if you plan to change your Mac's firewall settings, first use a tool, such as FonePaw MacMaster, to find and remove the junk files that exist on your system. FonePaw MacMaster can scan all your hard drives and compile the applications installed on your computer. This program is also able to identify the apps that are not working properly or those that are outdated so that you can remove them easily.
1. Download and launch MacMaster on your computer. (Free download)
Free try
2. Click on the “Uninstaller” tab.
3. Click “Scan” and the software will display all the applications installed on your computer. Select the apps you want to remove from the list. Apps can be sorted by name, size, selection, and last launched date to make it easier to find.
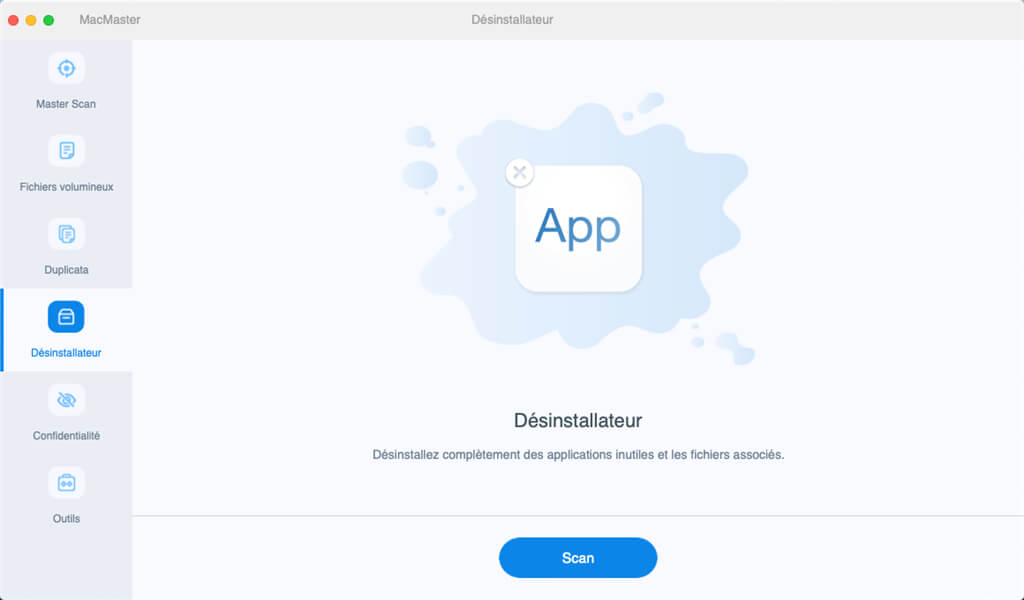
4. Click the “Clean” button and enter your administrator password when prompted.
The selected apps will now be completely removed from your system.
Now that this is done, you can turn your firewall on or off.
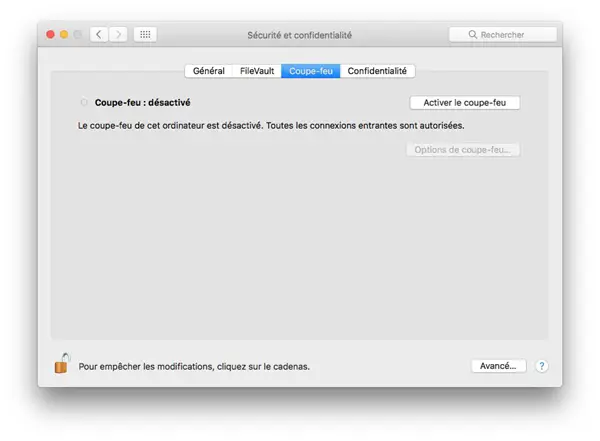
How to turn on the firewall on a Mac
1. Open “System Preferences” by clicking on the gear icon on your dock (usually it's to the right).
2. Click on “Security and Privacy”, which is in the first row of icons.
3. Go to the “Firewall” tab.
4. Click the padlock icon in the lower left corner of the window and enter your administrator password.
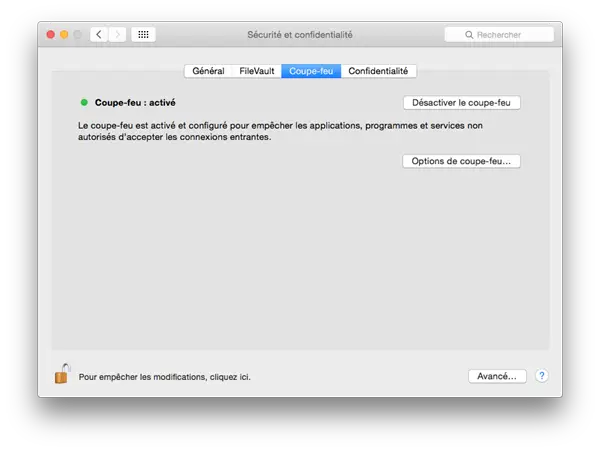
5. Click “Turn on firewall” (or “Start in OS X”).
Advanced settings
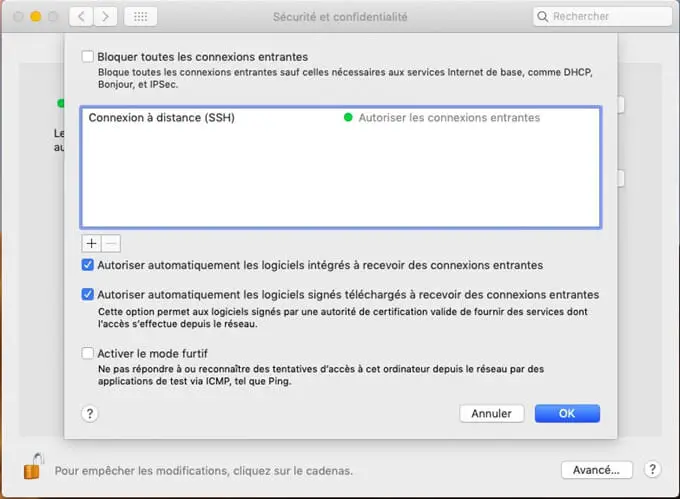
Block all incoming connections
If you select the option “Block all incoming connections”, it will prevent all sharing services, such as file sharing and screen sharing, from receiving incoming connections. The only system services that will always be allowed to receive incoming connections are:
- configd, which implements DHCP and other network configuration services
- mDNSResponder, which implements Bonjour
- racoon, which implements IPSec
To use sharing services, make sure the “Block all incoming connections” option has not been selected.
Allow specific apps
To allow a specific application to receive inbound connections, add it to the list using the firewall options:
1. Open “System Preferences”.
2. Click on the “Security” or “Security and Privacy” icon.
3. Select the “Firewall” tab.
4. Click the padlock icon in the preferences window, then enter an administrator name and password.
5. Click on the “Firewall options…” button
6. Click the (+) button to add an application.
7. Select the application for which you want to allow inbound connection privileges.
8. Click on “Add”.
9. Click on “OK”.
You can also remove the apps listed in the list that you no longer want to allow by clicking the (-) button.
Automatically allow embedded software to receive incoming connections
Software integrated by a valid certification authority is automatically added to the list of authorized applications, instead of requiring the user to authorize them. The applications included in OS X are integrated by Apple and are therefore allowed to receive inbound connections when this option is enabled. For example, since iTunes is already integrated by Apple, this software is automatically allowed to receive incoming connections through the firewall.
If you are running a non-integrated application that is not in the firewall list, a dialog box will appear with options to "Allow" or "Deny" connections for the application. If you choose "Allow", then OS X will integrate the application and automatically add it to the firewall list. If you choose "Deny" then OS X will add it to the firewall list but deny incoming connections intended for this application.
If you want to deny a digitally integrated app, you must first add it to the list and then explicitly deny it.
Some applications check their own integrity when they are opened without being allowed in the firewall. If the firewall recognizes such an application, it will not be integrated. Instead, the "Allow" or "Deny" dialog box will appear whenever the application is opened. This can be avoided by switching to a version of the application integrated by its developer.
Activate stealth mode
Enabling stealth mode prevents the computer from responding to scan requests. The computer still responds to incoming requests from authorized applications, but unexpected requests, such as ICMP (ping), will be ignored.
Firewall limits
The firewall application is designed to work with the Internet protocols most commonly used by applications - TCP and UDP. Firewall settings do not affect AppleTalk connections. The firewall can be configured to block inbound ICMP pings by enabling stealth mode in advanced settings. Earlier ipfw technology was still accessible from the command line (in Terminal) and the firewall application does not block any rules defined with ipfw. If ipfw blocks an incoming packet, the application's firewall will not process it.